Proof of Authority (PoA) is an alternative consensus mechanism that can provide higher scalability than Proof of Work or Proof of Stake. How does PoA achieve that level of scalability? Which blockchains implement this consensus mechanism? Check out the full explanation in the following article.
Article Summary
- ⚡ The Proof of Authority is a consensus method that gives a designated individual or group the power to validate transactions and create a new block in the blockchain.
- 🖥️ The way PoA works involves selecting authority nodes or validators that have the power to validate and authorize transactions.
- 🏆 PoA has better scalability and energy efficiency than PoS and PoW but worse decentralization than PoS and PoW.
What is Proof-of-Authority?
The Proof of Authority is a consensus method that gives a designated individual or group the power to validate transactions and create a new block in the blockchain. The PoA consensus algorithm utilizes identity values. It means block validators are staking their own reputation rather than tokens or guessing the hash target.
In PoA, the validator must have a clear and verified identity. This differs from Proof-of-Work (PoW) or Proof-of-Stake (PoS) mechanisms, where anyone can become a validator without needing to reveal their identity.
The PoA mechanism was the idea of Gavin Wood, co-founder of Ethereum, as a solution for faster and more energy-efficient transaction processing, especially for private blockchains. This is because PoA only requires a small number of validators. This inevitably makes the PoA mechanism much more energy-efficient than the PoW mechanism. In terms of scalability, it is also superior to both PoW and PoS mechanisms.
Despite having better scalability, the smaller number of validators in PoA makes it more centralized. A concept that contradicts the idea of a decentralized blockchain. Additionally, the fact that validators in PoA are handpicked makes this mechanism less suitable for public blockchains.
You can also learn about the Proof-of-Stake mechanism in the following article.
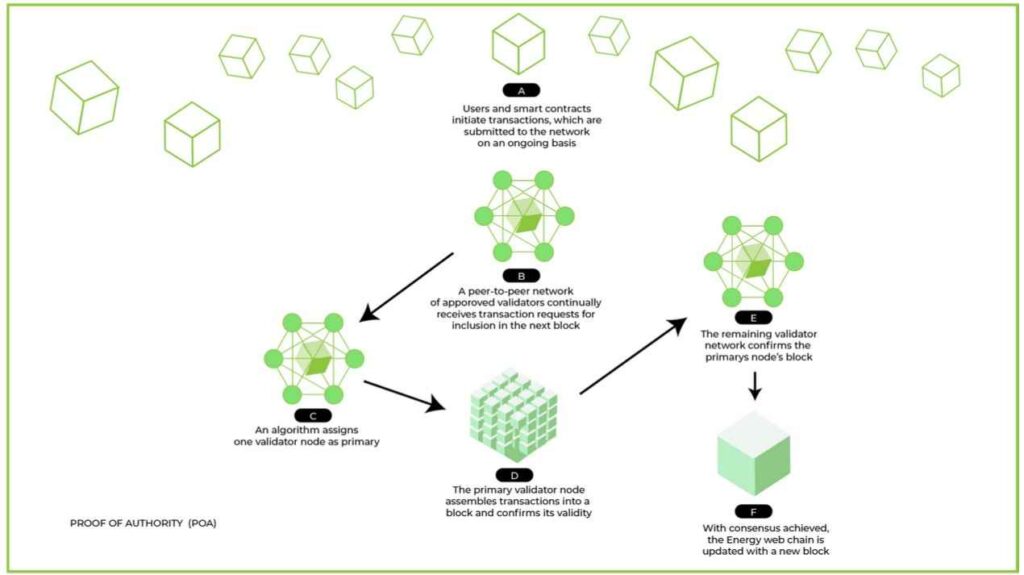
How Proof-of-Authority Works
The way PoA works involves selecting authority nodes or validators that have the power to validate and authorize transactions. These authority nodes are usually trusted entities, which can be individuals, groups, or institutions. To become authority nodes, each system may have different requirements. However, in general, the requirements are as follows:
- Validators must be trustworthy, have good moral standards, and without any criminal record.
- The validator’s real identity must be verifiable on the network and in the real world.
- Candidate validators must be willing to invest money and put their reputation on the line.
Candidates will undergo a rigorous selection process to reduce the risk of selecting questionable validators and encourage their long-term commitment.
In PoA, when a user submits a transaction, one or more randomly selected authority nodes will be responsible for validating the transaction. Upon successful validation, the transaction will be added to a new block. Authority nodes are also in charge of creating new blocks and adding them to the blockchain.
Trust in PoA is based on the reputation and reliability of authority nodes. If an authority node breaks the rules or commits an unethical act, its reputation will be tarnished, and it may be removed from the network.
Advantages of Proof-of-Authority
- ⚡ Energy Efficient. As there are far fewer validators and no mining is required, PoA does not require many energy resources.
- 💨 Scalability. In terms of scalability, PoA can also process transactions faster. Making it more efficient than PoW and even PoS.
- 🔒 Security. With strict background checks and the selection of potential validators, it can make PoA as secure as PoW and PoS. The selection of validators also frees PoA from the threat of 51% attacks.
Scalability is one aspect of the blockchain trilemma. Please find out more about it here.
Disadvantages of Proof-of-Authority
- 🖥️ Centralized. With a limited number of selected validators, PoA is more centralized than PoW and PoS.
- ⚖️ Open information. The disclosure of validators’ identities poses a threat to third parties who might manipulate them. For example, irresponsible parties may influence PoA validators to act dishonestly to corrupt the system from within.
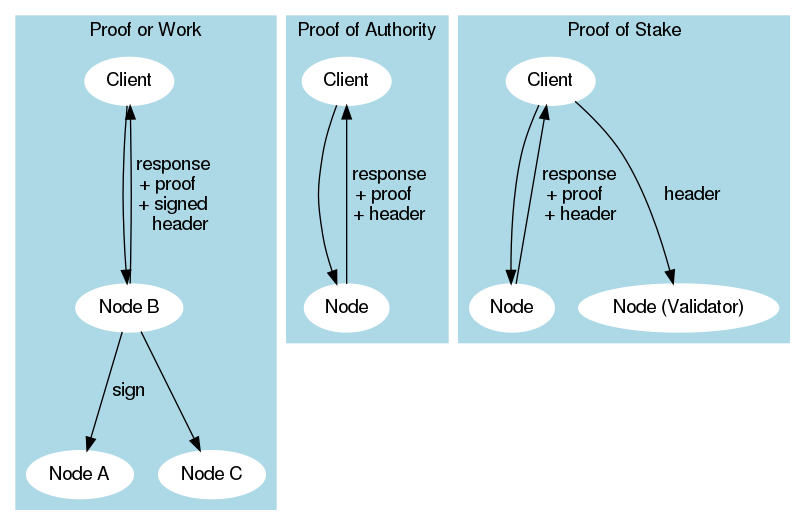
Proof of Authority vs Proof of Work vs Proof of Stake
| PoA | PoW | PoS | |
|---|---|---|---|
| Validator Selection | Rigorous selection | Randomly | Randomly |
| Validator Identity | Public | Anonymous | Anonymous |
| Stake | Reputation | Computing power | Token |
| Scalability | Highest | Lowest | Moderate |
| Energy Consumption | Most efficient | Least efficient | Moderate |
| Use Cases | Private blockchain | Public blockchain | Public blockchain |
Examples of Blockchains that Use Proof-of-Authority
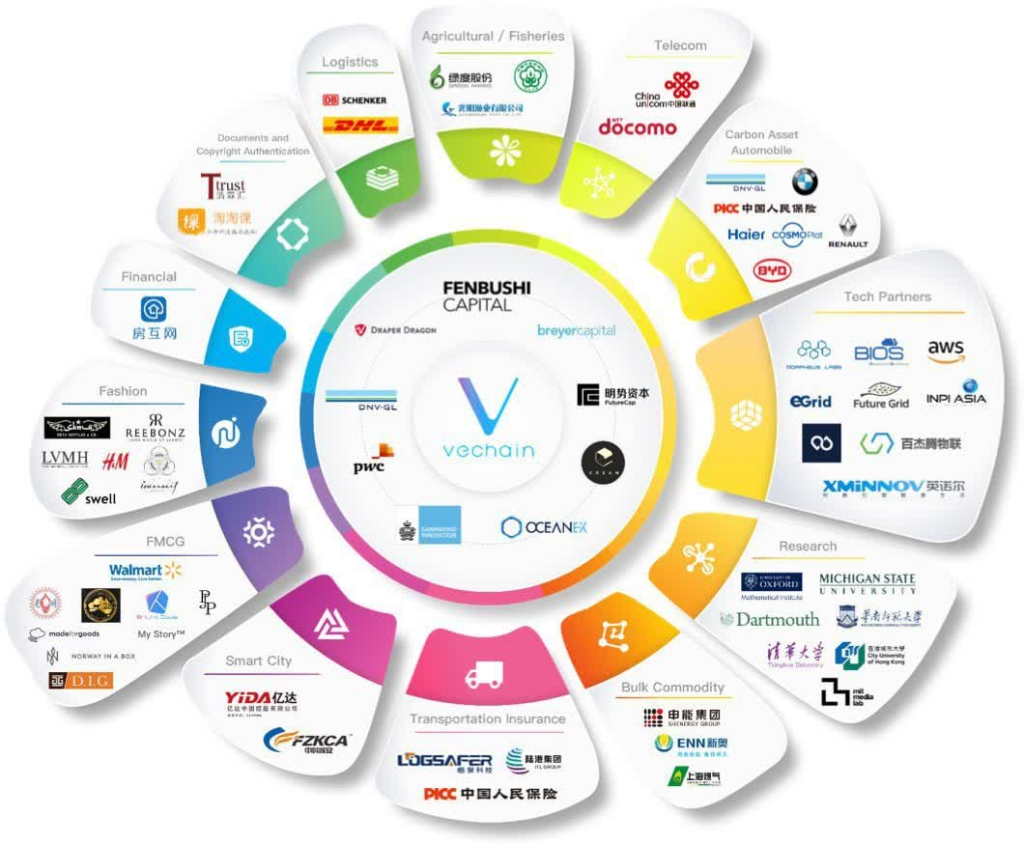
VeChain is one of the blockchains that uses the PoA mechanism. VeChain is a blockchain that aims to improve supply chain management, including product tracking and monitoring, product quality verification, and inventory level management. VeChain’s decentralized network enables the integration of the Internet of Things (IoT) to share and analyze data in real-time. It is increasing efficiency and better transparency for businesses.
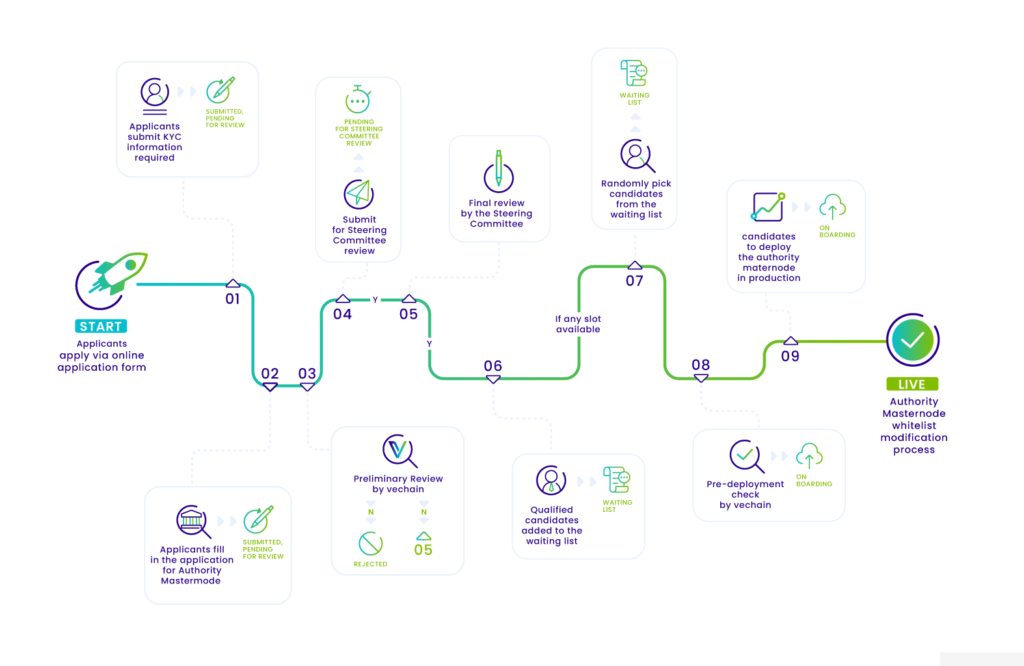
Specifically, the VeChainThor blockchain functions similarly to other business blockchain platforms. However, the difference is that VeChainThor offers a more integrated and efficient blockchain solution through its Blockchain as a Service (BaaS) product called ToolChain. The validators that verify transactions and generate blocks on VeChain are called Authority Masternodes (AM).
The number of nodes in VeChain is only 101, compared to Bitcoin’s 16.400 and Ethereum’s 5.750. VeChain can increase the efficiency necessary for commercial and industrial needs by sacrificing decentralization.
Pintu Academy has prepared an article that dives deep into VeChain and its technology here.
Conclusion
Each consensus mechanism, be it PoA, PoW, or PoS, has its benefits and advantages. The blockchain and crypto industry that glorifies decentralization makes the concept of PoA counterintuitive. But on the one hand, PoA sacrificing decentralization allows it to process transactions faster. This makes the PoA approach attractive and a solution for some groups. As a result, PoA is a consensus mechanism more suitable for private blockchains rather than public blockchains.
Buy Crypto Assets in Pintu
Before you start staking, you can buy a variety of token assets such as ETH, SOL, ADA, and others safely and easily at Pintu. Pintu diligently evaluates all its crypto assets, highlighting the significance of being cautious.
Pintu is also compatible with popular wallets such as Metamask to facilitate your transactions. Download Pintu app on Play Store and App Store! Your security is guaranteed because Pintu is regulated and supervised by Bappebti and Kominfo.
Aside from buying and trading crypto assets, you can expand your knowledge about cryptocurrencies through various Pintu Academy articles. Updated weekly, all Pintu Academy articles are made for knowledge and educational purposes, not as financial advice.
References
- Mike Antolin. What Is Proof-of-Authority? Coin Desk, accessed on 22 June 2023.
- Coin Telegraph, Proof-of-authority vs. proof-of-stake: Key differences explained, accessed on 22 June 2023.
- Anders Bylund, What is Proof of Authority (PoA)? The Motley Fool, accessed on 22 June 2023.
- Jagit Singh, What is VeChain (VET) and how does it work?, Cointelegraph, accessed on 22 June 2023.